In a surprising turn of events, the notorious BlackCat ransomware group—also known as ALPHV—experienced a significant operational disruption recently, with its dark web portal going offline for over 48 hours. This downtime has triggered waves of speculation among cybersecurity experts and law enforcement agencies alike. Is this a takedown, an internal restructuring, or a sign of something bigger?
Who Is BlackCat (ALPHV)?
BlackCat is one of the most sophisticated ransomware-as-a-service (RaaS) groups in operation today. Known for their advanced encryption methods and a reputation for targeting high-value institutions, BlackCat rose to prominence in the post-REvil and Conti era. Their tools are written in Rust, a programming language favored for performance and evasion.
Key Features of BlackCat’s Modus Operandi:
- Use of Rust for stealth and cross-platform attacks
- Double-extortion model (data encryption + data leak threats)
- Affiliate-based RaaS structure
- Targeting critical sectors like education, healthcare, and infrastructure
What Happened Recently?
Reports began surfacing across threat intelligence platforms and Telegram channels that BlackCat’s primary leak site had become unreachable. At first, many assumed it was a temporary glitch. But as hours turned into days, the narrative shifted. Analysts speculated on potential causes, ranging from law enforcement takedown to technical overhaul.
Top Theories Behind the Outage
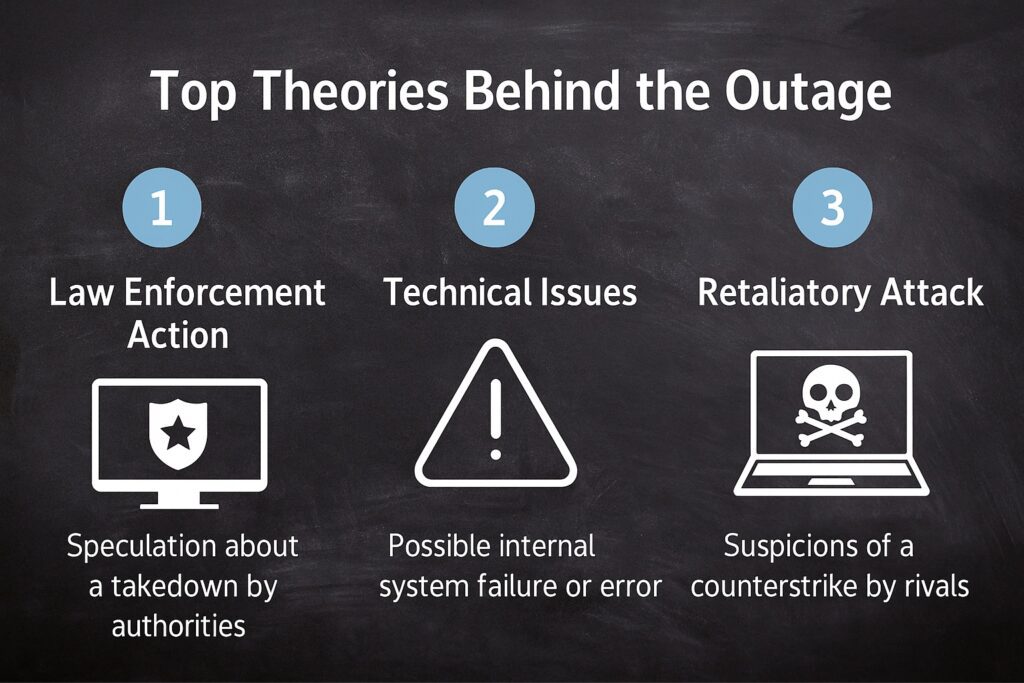
1. Law Enforcement Intervention
The most optimistic theory among cybersecurity professionals is a coordinated action by international law enforcement—perhaps led by the FBI or Europol. This would follow the pattern seen in earlier takedowns of groups like REvil and NetWalker.
2. Internal Reboot or Migration
Another plausible theory is that BlackCat is proactively migrating their infrastructure to a more resilient architecture. Some believe this could be an upgrade to withstand increasing surveillance or counter-actions from authorities and cyber firms.
3. Retaliatory DDoS Attacks
Some members of the cybersecurity community suggest that rival threat actors or even vigilante hackers might have initiated a DDoS (Distributed Denial of Service) campaign to disrupt the group’s operations.
How Victims Were Affected
Interestingly, the outage left many current victims in limbo. These organizations were in the middle of negotiating ransom payments or awaiting decryption keys. Without access to BlackCat’s portal, they faced additional uncertainty—raising concerns over business continuity and data restoration.
Key Risks for Victims:
- Inability to pay ransom or retrieve decryptors
- Increased chances of data being leaked elsewhere
- Legal and compliance complications due to stalled negotiations
What This Means for Cybercrime Operations
This event is more than a temporary blackout. It could signify a larger shift in the cybercriminal ecosystem. Cyber gangs are becoming increasingly agile—adapting not just in terms of malware sophistication but also in their operational tactics and infrastructure resilience.
Expect the Following Trends:
- Increased use of decentralized hosting and blockchain domains
- Enhanced fallback mechanisms in ransomware platforms
- More fluid affiliate relationships and migration between groups
Responses from the Cybersecurity Community
Organizations like CISA, FBI Cyber Division, and global cybersecurity firms have all acknowledged the event but haven’t released official statements yet. Threat intelligence vendors continue to monitor the dark web for signs of activity or re-emergence under a different name.
Implications for Enterprises and Defenders
If you’re a business owner, security professional, or CISO, here’s what this incident should signal to you:
- Prepare for more resilient and evasive ransomware tactics
- Ensure your response plan prepares for disrupted communications during a cyberattack.
- Stay informed through threat intelligence feeds and verified sources
Learn more about protecting your systems in our related guide: What Is Ransomware and How to Protect Yourself.
Could This Be the Beginning of the End?
While it’s tempting to celebrate a ransomware group going dark, cybersecurity veterans know better. These groups often return stronger, more distributed, and harder to trace. This could be the calm before a rebrand or the emergence of an even more aggressive successor.
Historical Context: How Ransomware Groups Evolve
To understand the importance of this event, it’s helpful to look at the historical behavior of ransomware groups. Notorious outfits like REvil, DarkSide, and Conti all followed similar trajectories—rising fast, earning notoriety, then either being disrupted or going underground, only to reemerge under new names.
In 2021, the DarkSide gang was allegedly behind the major attack on Colonial Pipeline. After global attention and pressure, the group went silent, only for some of its affiliates and infrastructure to reappear in newer operations like BlackMatter and eventually BlackCat.
This cycle of rebranding and adapting helps ransomware actors avoid prosecution, evade sanctions, and stay one step ahead of defenders.
What Can Organizations Learn From This Disruption?
While it’s easy to view these disruptions as victories, smart organizations treat them as teachable moments. Here are several key takeaways for businesses and cybersecurity teams:
- Never Rely on Criminal Platforms: If you’re negotiating or handling an incident, always assume the attacker’s infrastructure could disappear. Maintain offline copies of communication and instructions.
- Invest in Threat Intelligence: Subscribe to reliable threat intelligence services that can inform you of shifts like this as they happen.
- Prepare for Silent Periods: Have a response plan that accounts for attacker silence. If the leak site goes down mid-negotiation, your company must know how to proceed.
- Use the Downtime: If a ransomware group is inactive, use that time to patch vulnerabilities they’ve targeted, conduct post-incident analysis, and improve detection capabilities.
How Governments Are Responding Globally
Governments across the globe have ramped up their cybersecurity initiatives, especially targeting ransomware-as-a-service groups like BlackCat. The U.S. government’s Ransomware Initiative includes collaborations with allies, improved cyber regulations, and financial sanctions on crypto exchanges used by cybercriminals.
Additionally, joint task forces between the U.S., UK, Australia, and other countries have shown promise in disrupting cybercriminal ecosystems. While not every disruption is publicized, intelligence-sharing between countries has increased dramatically since 2022.
Signs of a BlackCat Rebrand?
Speculation continues that the outage is a precursor to a rebrand. Historically, ransomware groups often change names to evade sanctions and reinvent their image. Security researchers have already spotted new infrastructure possibly linked to BlackCat affiliates under different monikers.
Some potential indicators of a rebrand include:
- Similar encryption algorithms reused in new malware strains
- Ransom notes with comparable language and demands
- Domain registration using familiar TLDs or previously observed WHOIS patterns
- Leak sites that mirror the UI or structure of BlackCat’s former platform
Future-Proofing Against Evolving Ransomware Threats

As ransomware groups continue to adapt, businesses must also evolve their defense strategies. Here are practical steps that organizations should take immediately:
- Backup Strategy: Maintain multiple, tested backups across different locations (including offline backups).
- Zero Trust Security: Implement a zero-trust framework that reduces lateral movement inside networks.
- EDR/XDR Solutions: Use advanced threat detection tools with behavioral analytics.
- Employee Training: Most attacks start with phishing. Regularly educate employees to spot and report suspicious activity.
- Incident Simulation: Run tabletop exercises to ensure all teams know how to respond to ransomware incidents efficiently.
The Role of Cyber Insurance in a Post-Ransomware World
With ransomware attacks growing both in frequency and sophistication, many organizations are turning to cyber insurance as a safety net. However, recent events, including incidents involving BlackCat and other groups, have reshaped the cyber insurance landscape dramatically.
Some insurers are now imposing stricter requirements before issuing policies, such as:
- Mandatory multi-factor authentication (MFA)
- Proof of employee training programs
- Regular vulnerability scanning and penetration testing
- Documented incident response and backup plans
While insurance can offer some financial relief, it’s not a silver bullet. Many policies do not cover the full extent of damages, and in some cases, paying a ransom may be legally restricted due to sanctions on certain groups.
Dark Web Activity During the Outage
Cybersecurity researchers who monitor dark web forums noted a sharp decline in chatter from known BlackCat affiliates during the outage. Interestingly, some threads speculated about “leadership conflicts” within the group, suggesting that internal turmoil could be a contributing factor.
Others speculated that BlackCat’s administrators were attempting to spin up a new infrastructure on emerging decentralized platforms—ones that are more resistant to takedowns due to their peer-to-peer nature. This shift, if confirmed, would represent a new frontier in cybercrime logistics.
The Importance of Community Sharing and Collaboration
Events like the BlackCat disruption highlight the value of shared intelligence across the cybersecurity community. Public-private partnerships have proven crucial in tracking, disrupting, and even deterring threat actors. One excellent example is the Joint Cyber Defense Collaborative (JCDC), a U.S.-led initiative involving major tech firms, infrastructure providers, and federal agencies.
By sharing anonymized telemetry, attack signatures, and behavioral indicators, organizations can significantly reduce response times and prevent the spread of ransomware threats. Working together is essential for moving from a reactive stance to a proactive cybersecurity approach.
Frequently Asked Questions (FAQ)
Conclusion
While we may not yet know the full story behind BlackCat’s disappearance, the disruption itself offers plenty of insight. It’s a case study in the fragility and volatility of even the most advanced criminal enterprises—and a call to action for defenders everywhere.
The cybersecurity landscape is constantly shifting. What matters most is how quickly we adapt. Let this moment be a reminder that vigilance, preparedness, and collaboration are the true pillars of digital defense.
For more resources on how AI is intersecting with cybersecurity, check out our guide: AI-Powered Cyberattacks: 2025 Cybersecurity Trends.